We are still looking for one to two postdoctoral researchers to complement our research group at Paderborn university. For further information, please consult our previous announcement here. As stated, please direct your applications to se-jobs.cs@upb.de
We are still looking for one to two postdoctoral researchers to complement our research group at Paderborn university. For further information, please consult our previous announcement here. As stated, please direct your applications to se-jobs.cs@upb.de
If you have a deep interest in software engineering, especially software security, the I am very much looking forward to your application! In particular, I am interested in candidates with a proven track record (at least two papers at very reputable venues) in any of those subject areas:
- Static and/or dynamic program analysis
- Software Security
- Systems Security
- Applied (!) cryptography and/or cryptanalysis

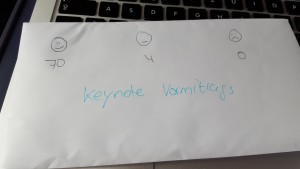
 Attending
Attending